Studying for Security+ Exam
Big kudos to fishlover7!
Redditor fishlove7 put in serious work crafting the Ultimate CompTIA SY0-701 Security+ Study Guide. The fish’s real name? Christian Joseph Miranda as it is written in the very first page of a study guide! Please give him a upvote in this Reddit link; the guide is included there too.
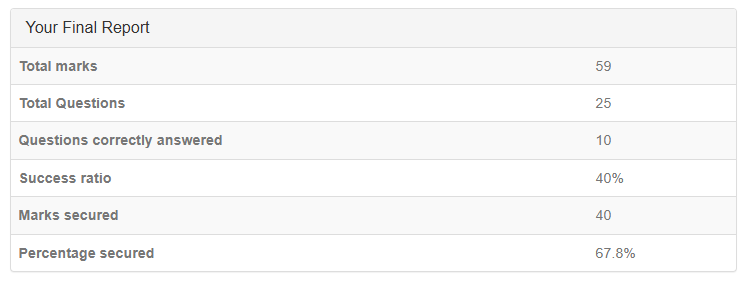
There are about 15 lessons in that study guide with 437 pages. I will not be noting down everything here. I blog the key takeaways I think are worth remembering from the study guide. I will also measure my knowledge by answering all questions from here ExamCompass. As a matter of fact, I will do one right now to see how I do. I’ve been a QA for 4 years and a Pen Tester for a year.
Whelp! I didn’t do well. ExamCompass has about 24 different quizzes, each with 25 questions. The actual Security+ exam… its 90 questions in 90 minutes. Basically a minute per question. Most are multiple choices. Some will ask you to select 3 answers out of five which really slows things down. If got two right and one wrong, then the whole question is counted as wrong. Gotta to know your stuff to breeze through quickly.
Each Security+ post here will focus on one or few lessons, plus a ExamCompass quiz. I did quiz 1 today and I noted down what I learned from it.
ExamCompass Quiz 1 notes:
describe technical security controls:
1) Sometimes called logical security controls <— I got this right
2) Executed by computer systems (instead of people) <— I didn’t select this
3) Implemented with technology <— I got this right
technical security controls examples:
1) Encryption <— I got this right
2) IDS <— I didn’t select this
3) Firewalls <— I got this right
describe managerial security controls:
1) Also known as administrative controls <— I got this right
2) Focused on reducing security incidents <— I didn’t select this
3) Documented in written policies <— I got this right
describe managerial security controls:
1) Also known as administrative controls <— I got this right
2) Focused on reducing security incidents <— I didn’t select this
3) Documented in written policies <— I got this right
managerial security controls examples:
1) Organizational security policy <— I got this right
2) Risk assessments <— I got this right
3) Security awareness training <— I got this right
describe operational security controls:
1) Focused on the day-to-day procedures of an organization <— I didn’t select this
2) Used to ensure that the equipment continues to work as specified <— I got this right
3) Primiarily implemented and executed by people (opposite to computer system) <— I got this right
operational security controls examples:
1) Configuration management <— I didn’t select this
2) System backups <— I got this right
3) Patch management <— I got this right
which refers to security controls designed to deter, detect, and prevent unauthorized access, theft, damage, or destruction of material assets?
incorrect answer: managerial security controls
correct answer: physical security controls
NOT EXAMPLES of physical security controls:
1) Data backups <— I got this right
2) Firewalls <— I got this right
3) Asset management <— I got this right
physical security controls examples:
1) Lighting
2) Access control vestibules
3) Fencing/Bollards/Barricades
4) Security guards
preventive security controls examples:
1) Ecryption <— I got this right
2) Firewalls <— I got this right
3) AV software <— I got this right
deterrent security controls examples:
1) Warning signs <— I got this right
2) Lighting <— I didn’t select this
3) Fencing/Bollards <— I didn’t select this
which refers to detective security controls:
1) Log monitoring <— I got this right
2) Security Audits <— I got this right
3) CCTV <— I didn’t select this
4) IDS <— I didn’t select this
5) Vulnerability scanning <— I got this right
which refers to corrective security controls:
1) Recovering data from backup copies <— I got this right
2) Applying software updates and patches to fix vulnerabilities <— I got this right
3) Developing and implementing IRPs to respond to and recover from security incidents <— I didn’t select this
4) Activating and executing DRPs to restore operations after a major incident <— I got this right
which refers to compensating security controls:
1) Backup power system <— I got this right
2) MFA <— I didn’t select this
3) Application sandboxing <— I got this right
4) Network segmentation <— I got this right
term “Directive security controls” refers to the category of security controls that are implemented through policies and procedures:
answer: true <— I got this right
which terms fall into category of directive security controls:
1) IRP <— I got this right
2) AUP <— I didn’t select this
which terms describe the basic principles of information security:
1) CIA <— I got this right
“Non-repudiation” descirbes inability to deny responsibility for performing a specific action. In context of data security, non-repudiation ensures data confidentiality, provides proof of data integrity, and proof of data origin:
answer: false <— I didn’t select this
Which best applies to the concept of non-repudiation:
answer: Digital certificate <— I got this right
which type of user account violates the concept of non-repudiation:
answer: Shared account <— I didn’t select this
Each A in AAA stands for:
1) Authenication, verification of identity of a person or process <— I got this right
2) Authorization, granting or denying access to resources <— I got this right
3) Accounting, tracking accessed services and logging consumption <— I got this right
which solutions provide AAA functionality:
1) TACACS+ <— I didn’t select this
2) RADIUS <— I got this right
in context of AAA framework, common methods for authenticating people include:
1) Usernames and passwords <— I got this right
2) Biometrics <— I got this right
3) MFA <— I got this right
Which answers refer to common methods of device authentication used within AAA framework:
1) Digital certificates <— I didn’t select this
2) IP addresses <— I didn’t select this
3) MAC addresses <— I didn’t select this
I must have misread the last question. I overlooked “device”, answers are pretty obvious.